Updated February 24, 2026
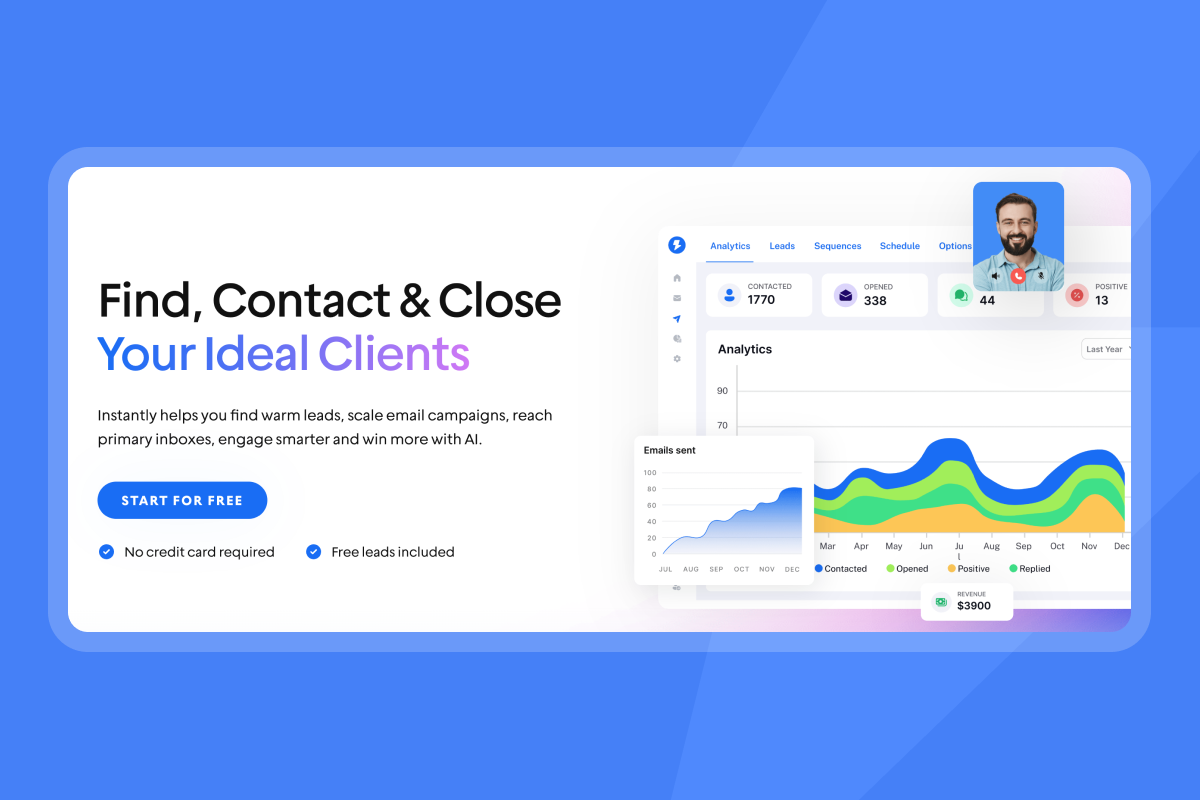
TL;DR: The Model Context Protocol (MCP) connects AI assistants directly to your Instantly account to automate reporting and campaign tasks. Out-of-the-box configurations often expose API keys, grant excessive permissions, and skip audit logging. Secure your integration by implementing OAuth 2.1 with bearer tokens, enforcing least-privilege API scopes, rotating credentials every 90 days, and conducting a Data Protection Impact Assessment for GDPR compliance. Without these controls, you risk exposing client lead data, violating privacy agreements, and burning your agency's reputation.
In April 2025, security researchers analyzing MCP found that most implementations grant AI assistants excessive permissions by default. Your team is likely already using AI to query campaign data or draft sequences. If you're using Instantly as your cold email solution, that data is only as protected as the integrations you build around it.
The Model Context Protocol allows AI to reach into your Instantly account and perform actions like pulling analytics, updating leads, or launching campaigns. This guide details the security architecture required to integrate AI agents safely into your cold email campaign infrastructure, covering authentication frameworks, API V2 scope controls, and GDPR compliance steps.
Understanding the Model Context Protocol (MCP) ecosystem
The Model Context Protocol gives AI assistants a standardized way to connect to data systems like your Instantly account, CRM, and file storage. Anthropic open-sourced MCP to provide a universal integration standard for AI applications.
Think of MCP like a USB-C port for AI applications. Just as USB-C provides a universal connection for electronic devices, MCP provides a standardized way to connect AI to your business tools. Without this standard, every AI tool would need custom integrations for every platform, creating maintenance overhead and security gaps.
Development platforms now support MCP, making it easier for your team to connect AI to your Instantly workspace without asking IT. For Instantly users, this means an AI assistant can query your campaign analytics, pull lead data from SuperSearch, or update lead data status directly through the API.
Instantly's official MCP documentation walks you through connecting Claude Desktop and other AI clients to your workspace. Setup takes minutes. However, connecting an AI is not the same as securing it. The Model Context Protocol is transport-agnostic and does not enforce authentication by default.
To learn more of the basic concepts about MCPs, check out the video guide below: For a practical walkthrough of what's possible once connected, see the guide on automating sales operations with the MCP server before locking down your security architecture.
The hidden risks: Shadow servers and unauthorized AI access
MCP servers depend on credentials like OAuth tokens and API keys for authentication. If an attacker steals one, they can impersonate the server and operate with legitimate access. A stolen API key to your Instantly account could allow them to read campaign data, export lead lists, or modify sequences without any login prompt.
Shadow MCP servers and attack vectors:
Your team members can spin up "shadow MCP servers" without going through your security review. This often happens when someone wants to automate a task and connects Claude Desktop to Instantly using their personal API key. Many MCP implementations request wide permission scopes so the AI "just works." That single server can access email accounts, lead databases, campaign settings, and analytics.
Because servers often hold multiple tokens, compromising one server can expose a wide range of systems. If an attacker compromises that server or intercepts the long-lived token, they can pivot fast. They can read your SuperSearch lead database, access campaign templates, or set up forwarding rules to siphon client data.
Security researchers have identified that MCP lacks native human-in-the-loop reviews, leaving high-risk actions without oversight. If attackers manipulate prompts and exploit injection points, the model can perform harmful actions like altering database records without authorization or forwarding sensitive documents to attacker-controlled addresses. Researchers have demonstrated credential exfiltration by exploiting MCP channels.
When you connect an AI to Instantly via MCP, you may be creating a data processing relationship that requires a Data Processing Agreement under GDPR. If the AI provider's terms allow them to use your data for training, you may be violating consent obligations to your leads.
Want to know more about common risks MCP server users might face? Check out the guide below for more info:
MCP server authentication security best practices
The MCP Authorization specification should be read alongside OAuth 2.0 security best practices. Many MCP implementations still use insecure defaults that conflict with enterprise security practices. The fixes below close those gaps.
Recommended authentication methods:
Use these authentication approaches based on your deployment context:
- OAuth 2.1 with PKCE (High security)
Best for production MCP servers. Standards-based with refresh token rotation and sender-constrained tokens. Trade-off: complex initial setup. - Bearer Tokens via Instantly API V2 (Medium-High security)
Best for direct Instantly API connections. Simple implementation with granular scopes. Trade-off: requires secure storage and 90-day rotation. - JWT (JSON Web Tokens) (Medium security)
Best for internal services. Self-contained and stateless verification. Trade-off: larger token size and revocation complexity. - Static API Keys (Low security)
Development and testing only. Easy to implement. Trade-off: no rotation capability and persistent risk if leaked.
RFC 7636 outlines PKCE (pronounced 'pixie'), which protects clients incapable of holding secrets from an entire class of attacks. PKCE is recommended for all clients using the Authorization Code grant.
Token management: UUIDs and lifecycle:
You should generate session IDs like UUIDs using secure random number generators. Avoid predictable or sequential session identifiers that could be guessed by an attacker. Bind each session ID to a specific user by combining it with their internal user ID. This ensures that even if an attacker guesses a session ID, they cannot impersonate another user.
Token rotation strategy:
Rotate API keys at least every 90 days. Key rotation limits the lifespan of compromised keys, reducing the blast radius if one leaks. Set up automated rotation from the start so you can respond quickly when an employee leaves or a token is exposed. If you have a strong automated process, you can rotate much more frequently.
Implementing least privilege:
The Principle of Least Privilege requires that every module access only the information and resources necessary for its legitimate purpose. The privileges associated with an access token should be restricted to the minimum required for the particular application.
For Instantly integrations:
- Reporting bot: Only
analytics:readscope, notcampaigns:deleteorleads:update - Campaign creation assistant:
campaigns:createandleads:createscopes but notapi_keys:deleteor billing access - Lead enrichment tool:
leads:updatebut neveraccounts:deleteorworkspaces:update
By scoping each MCP integration to only what it needs, you limit the blast radius if compromised.
Instantly API security: A deep dive into V2 protection
Instantly launched API V2 with enhanced security to address scale and security concerns that agency operators face. API Scopes give you granular control over each key's permissions. You can create multiple API keys with different privileges and revoke any key instantly if compromised.
Granular API scopes:
API Scopes enable granular control over API keys and their usage. The available scopes include all:all, all:create, all:read, all:update, all:delete, ai_agents:all, ai_agents:create, ai_agents:read, ai_agents:update, ai_agents:delete, and over 168 more covering campaigns, leads, accounts, analytics, workspaces, and email verifications.
When creating a key for an MCP reporting bot, select only campaigns:read and analytics:read. Avoid the all:all scope, which grants unrestricted access.
Bearer token implementation:
Bearer tokens work by including a token in the Authorization header of each API request in the format Authorization: Bearer YOUR_API_TOKEN. Unlike basic auth, bearer tokens are pre-issued and can be scoped to specific permissions, so you never send your account password with API calls.
When you create an API key in Instantly's developer portal, you select which scopes that key has access to. You can create one key for your MCP reporting bot with only analytics:read and campaigns:read, and a separate key for lead enrichment with leads:update and email_verifications:create.
Client-side security risks:
Exposing your API key in client-side environments like browsers or mobile apps allows malicious users to take that key and make requests on your behalf. Always route requests through your backend server.
Three secure alternatives:
- Backend proxy: Route all Instantly API calls through your server that holds the key in environment variables
- Secrets management service: Use AWS Secrets Manager, Azure Key Vault, HashiCorp Vault, or Google Cloud Secret Manager
- Serverless functions: Deploy API proxy functions (AWS Lambda, Vercel Functions, Cloudflare Workers) that authenticate users separately
Rate limiting:
Instantly applies rate limits at the workspace level shared between API v2 and API v1. If you exceed the limit, requests fail with the 429 status code. Implement exponential backoff in your MCP server to handle 429 responses gracefully.
Key management best practices:
Experts strongly recommend environment variables as a proactive key safety measure. Store keys in .env files excluded from version control. Never hardcode API keys in source code. Committing an API key to source code is a common vector for credential compromise.
For production MCP servers, use dedicated secrets management services that provide audit logs and automatic rotation. Implement strict access controls on the server environment where keys are stored.
Ensuring GDPR compliance with MCP and AI agents
When you connect an AI agent to your Instantly account via MCP and handle EU lead data, you may create a data processing relationship that falls under GDPR. GDPR requires that your AI vendor can prove they comply with the regulation and protect data subject rights.
Core GDPR principles:
Your Data Processing Agreement with the AI vendor must specify the subject matter, duration, nature, and purpose of processing. It must list the types of personal data and categories of data subjects. The processor must act only under your documented instructions unless required by law, and must implement appropriate technical and organizational measures to protect the data.
Training vs. inference:
Inference means using a pre-trained AI model to process your prompt and return output. Training means using data to build or refine the model itself. When you send lead data through an MCP integration, that is inference. Your AI vendor's terms should guarantee that customer data submitted for inference will not be used for model training. If they train on your data, it could be memorized, reproduced in responses to other users, or violate confidentiality agreements.
Prohibited data types:
Instantly's Data Usage Terms prohibit using data that violates CCPA, CPRA, GDPR, FCRA, CAN-SPAM, or TCPA. You cannot process information subject to HIPAA. Instantly's privacy policy asks that you do not include sensitive personal information like government IDs, financial account numbers, or medical information.
Data categories you must never process via MCP: Protected Health Information (PHI) under HIPAA, payment card data (PCI-DSS), government-issued identification numbers, or data from children (COPPA).
For a broader view of how these obligations apply across your entire outreach stack, review the full breakdown of email API security and compliance requirements covering GDPR, CCPA, and CAN-SPAM.
Essential DPA clauses:
GDPR Article 28 mandates specific elements that every DPA must include:
- Subject matter, duration, nature, and purpose: "Processor will host, store, and process customer data submitted through the MCP integration for the duration of the subscription term plus 30 days post-termination, solely to provide AI inference services described in the Master Service Agreement."
- Types of personal data and subject categories: List data types your MCP server processes - contact information (names, emails, phone numbers), account credentials, campaign content, and usage analytics. Specify data subject categories like your customer's business contacts.
Your DPA must also require the processor to assist with security, breach notifications, and data subject rights requests, to delete or return data at contract end, and to hold sub-processors to the same obligations.
Instantly provides a Data Processig Agreement that covers their processing activities. When you add an AI vendor via MCP, you need a separate DPA with that AI provider covering their processing of your Instantly data.
Conducting a DPIA:
Complete a Data Protection Impact Assessment for each MCP integration that processes EU data. Document what data is processed, why it is necessary, the risks to data subjects, and your mitigation measures (OAuth 2.1, least-privilege scopes, encryption, audit logging, 90-day token rotation). Review the DPIA whenever you add new MCP integrations.
Instantly's Privacy Center provides resources for understanding your obligations, and you can request access to collected data to support subject access requests.
Checklist for MCP server security and GDPR compliance
Use this checklist before deploying any MCP integration with your Instantly account.
Authentication and access control:
- Implement OAuth 2.1 with PKCE for production MCP servers
- Create separate Instantly API keys for each MCP integration
- Store API keys in environment variables or secrets management services, never in source code
- Use non-deterministic UUIDs for session IDs bound to user context
- Implement token rotation every 90 days or less with automated processes
- Document all MCP servers and their owners to prevent shadow IT
Data protection and privacy:
- Complete a Data Protection Impact Assessment for each MCP integration processing EU data
- Sign a Data Processing Agreement with your AI vendor that covers their processing of Instantly data
- Verify AI vendor's policy prohibits using your data for training public models
- Ensure your MCP server never processes prohibited data types (PHI, PCI, government IDs)
- Review Instantly's DPA and ensure compliance with sub-processor requirements
- Implement data retention policies that delete MCP-processed data after purpose is fulfilled
- Enable audit logging to track API access and changes
Technical safeguards:
- Route all API calls through backend servers, never expose keys in client-side code
- Implement rate limiting and exponential backoff to respect Instantly's API limits
- Enable TLS 1.2+ for all data in transit between MCP server and Instantly
- Set up monitoring and alerts for unusual API activity or failed authentication attempts
- Test prompt injection scenarios to verify your MCP server rejects malicious instructions
- Document incident response procedures for token leaks or unauthorized access
- Regularly review and revoke unused API keys from Instantly's developer dashboard
Operational controls:
- Train team members on secure MCP practices and the risks of shadow servers
- Require security review before deploying new AI/MCP integrations
- Maintain an inventory of all MCP servers, their purposes, and data access scopes
- Conduct quarterly audits of API key usage and scope assignments
- Test your ability to revoke access immediately in emergency scenarios
- Review AI vendor's security posture and any sub-processors they use
- Document MCP architecture in data flow diagrams for compliance audits
For deeper implementation guidance, review Instantly's MCP documentation.
Audit your API keys today
Security enables scale. Most agencies view security as a blocker to AI adoption, but it is the foundation that lets you run automation safely. Lock down your MCP server with OAuth 2.1, least-privilege API scopes, and GDPR-compliant data handling, and you can scale AI-powered workflows across 100+ client campaigns without the constant fear of data leaks or compliance violations. Before applying these controls, make sure you've completed the initial setup, follow the step-by-step guide to connect your AI assistant to your cold email platform and then layer these security measures on top.
The agencies that win are those that treat client lead data like the asset it is. Review your Instantly API settings today. Identify any keys with all:all scope and replace them with least-privilege alternatives. Implement the security checklist above before your next AI integration. If you are scaling with advanced features like SISR or webhook monitoring, use our API V2 documentation to build secure, GDPR-compliant workflows.
Try Instantly free and apply these security controls from day one.
FAQs
Does Instantly use my lead data or campaign content to train public AI models?
No. Instantly processes customer data as a service provider under your instructions per their DPA and Terms.
How do I immediately revoke an MCP server's access to my Instantly account?
Log into your Instantly account, navigate to Settings → API, locate the specific API key used by that MCP server, and click "Delete" to terminate access instantly.
What happens if my Instantly API key is leaked?
Attackers can perform any actions permitted by that key's scopes until you revoke it. Log into your account, navigate to Settings → API, locate the compromised key, and click "Delete" immediately. Then review your audit logs to check for unauthorized activity.
Do I need a separate Data Processing Agreement with my AI vendor?
Yes. Instantly's DPA covers their processing, but when you connect an AI vendor via MCP, you need a separate DPA with that vendor covering their processing of your Instantly data.
Can I use MCP to process HIPAA or payment card data through Instantly?
No. Instantly's Data Usage Terms explicitly prohibit uploading PHI, payment card data, government IDs, or other sensitive categories.
How often should I rotate Instantly API keys used by MCP servers?
Rotate API keys at least every 90 days. If you have automated rotation processes, you can rotate more frequently to reduce exposure if a key is compromised.
Key terms glossary
Model Context Protocol (MCP): An open standard developed by Anthropic for connecting AI assistants to external data sources and tools through a unified interface, similar to how USB-C standardizes device connections.
Bearer Token: An authentication credential included in the Authorization header of API requests that grants access to resources without requiring repeated login credentials. Instantly's API V2 uses bearer token authentication.
UUID (Universally Unique Identifier): A 128-bit identifier generated using secure random number generators to create non-predictable session IDs that prevent attackers from guessing valid sessions.
API Scope: A permission setting that defines which specific operations an API key can perform, such as campaigns:read or leads:update, enabling least-privilege access control.
Data Protection Impact Assessment (DPIA): A GDPR-required process to identify and mitigate privacy risks when processing personal data through new technologies like AI/MCP integrations.
OAuth 2.1: An enhanced authorization framework that provides secure delegation of access rights through time-limited tokens, refresh token rotation, and PKCE to prevent interception attacks.
Least Privilege: A security principle requiring that each user, program, or system component has only the minimum access rights needed to perform its function, reducing the blast radius of breaches.
PKCE (Proof Key for Code Exchange): A security extension to OAuth that protects authorization codes from interception attacks, particularly important for applications that cannot securely store client secrets.





