Updated April 22, 2026
TL;DR: You need three pillars for B2B cold email compliance: a documented legal basis (usually Legitimate Interest for GDPR-covered outreach), clean data sourcing from vendors who can prove lawful collection, and airtight opt-out management that syncs across every tool your team uses. B2B rules differ meaningfully from B2C, which means many sales teams are applying the wrong framework. Get these three things right and deliverability improves, pipeline becomes predictable, and compliance audits stop being a fire drill.
Most sales teams obsess over email copy while ignoring the unvetted data sources that actively destroy their domain reputation. You can legally buy B2B email lists. What creates compliance exposure is buying from vendors who cannot document their sourcing methods, or sending to contacts without a defensible legal basis, which leads to spam flags, blacklists, and significant legal penalties.
This guide gives you the exact frameworks, vendor questions, and opt-out workflows to keep your domains safe and your pipeline full.
Why B2B email privacy matters for sales teams
Privacy compliance is not just a legal department problem. It directly affects your deliverability, and by extension your revenue. When your outreach lands in spam folders or triggers blocklist flags, monthly pipeline targets suffer directly.
Here's how it works: when you use unvetted lists, you hit spam traps and invalid addresses that drive up your bounce rates, damage your sender reputation with inbox providers, and cause your legitimate emails to land in junk folders. A reputation hit from one bad campaign can take weeks to recover from. The Ultimate Guide to Cold Email Deliverability from Instantly walks through how each of these variables compounds over time.
Unsafe sourcing: risks and reputation
When you use data from vendors who scrape, harvest from breached databases, or re-sell lists without proper consent documentation, you expose your organization to significant penalties. GDPR fines for severe violations can reach €20 million or 4% of global annual turnover, whichever is higher. CAN-SPAM penalties reach up to $53,088 per non-compliant email. CASL violations carry fines up to $10 million per violation.
Two concrete examples of non-compliant sourcing: a vendor who collects emails by scraping LinkedIn profiles without user permission, and a provider who buys bulk lists from data brokers that aggregate personal data without documenting lawful collection. Both practices expose you to risk even when you had no visibility into the upstream sourcing.
Trust prevents deliverability issues
When your data sourcing is transparent and your outreach is legally grounded, the downstream effects are measurable and compounding. Verified contacts produce lower bounce rates because the addresses are current and actively monitored. Lower bounce rates protect your sender reputation scores with inbox providers like Gmail, Outlook, and Yahoo, which track bounce patterns as a primary trust signal. Protected sender reputation means your emails reach the primary inbox rather than being filtered into spam folders or blocked entirely by algorithmic filters.
Consistent inbox placement drives more opens, more replies, and more predictable pipeline. Inbox providers use engagement signals, open rate, reply rate, and spam complaint rate, as trust proxies that reinforce or degrade your domain's standing over time. A list built on compliant sourcing produces the engagement patterns that strengthen those signals: contacts who recognize your value proposition are more likely to engage rather than mark you as spam.
Contrast this with what happens when sourcing is opaque or non-compliant. Spam trap hits and invalid addresses trigger algorithmic filters that suppress delivery across your entire sending domain, not just one campaign. A single campaign sent to a dirty list can poison your domain reputation for weeks, affecting every sequence your team runs during the recovery period. Clean sourcing is the upstream input that makes all of that possible.
"I appreciate Instantly for its intelligent handling of domain and mailbox rotation as well as provider matching, which is critical for ensuring that my emails land directly in the primary inbox instead of getting caught in spam filters." - Richard E. on G2

B2B vs. B2C email privacy rules
In B2C email marketing, you typically need explicit prior consent before sending any commercial message. B2B operates under different rules in most jurisdictions. The UK ICO's guidance on legitimate interests confirms that business contacts are more likely to reasonably expect the processing of their personal data in a business context, and that outreach is less likely to have a significant impact on them personally.
This distinction matters for how you structure your legal basis. In a B2B context, Legitimate Interest (a defined lawful basis under GDPR) is often more appropriate than explicit consent. First-party data (contacts who have directly shared their details with you) always carries stronger compliance standing than third-party purchased lists, and zero-party data (contacts who voluntarily submitted information through your own forms or events) typically carries even stronger standing.
Mastering B2B email consent protocols
You cannot treat B2B consent as a single checkbox. The framework you need depends on where your contact is located, what regulation governs the relationship, and how you collected the data.
The key distinction is between implied consent and explicit (express) consent. Both are valid under certain conditions, but they carry different documentation requirements and different risk profiles.
Getting verifiable opt-in consent
You have explicit opt-in when the contact took a proactive action to agree to receive communications, such as completing a form with a clear opt-in field or verbally confirming during a documented conversation. Under CASL, the CRTC defines express consent as the recipient taking an opt-in action, with you retaining a record of when and how that action occurred.
For purchased lists, you cannot retroactively claim explicit opt-in consent unless the vendor provides verifiable documentation that each contact opted in to receive commercial emails from third-party senders.
What is B2B implied consent?
You can use implied consent when the contact has a pre-existing relationship with your organization or has made their business email publicly available. Under CASL, implied consent scenarios include:
- A prior commercial transaction with the recipient.
- The recipient publishing their email address on a company website without a statement declining commercial contact.
- An existing non-business relationship, such as membership in the sender's own club, association, or voluntary organization.
Critically, if a business contact publishes their email publicly, the message must relate to their professional role or duties. A finance VP's email listed on a company website implies they can be contacted about finance-relevant products, but sending them a consumer promotion does not meet this standard.
Mandatory vs. optional consent scenarios
You must get explicit consent when sending to consumers in Canada under CASL, when no other lawful basis applies under GDPR, and when the email content has no clear connection to the recipient's professional role.
You can more commonly use Legitimate Interest for B2B cold email in GDPR-covered jurisdictions when reaching contacts at companies whose profiles match your ideal customer profile and who would reasonably expect to receive relevant outreach. CAN-SPAM does not require prior consent at all, but still imposes requirements on sender identification and opt-out processing.
Proving B2B email consent
Documentation makes the difference between a compliant program and one that only sounds defensible. Consent records should capture the date and method of consent, the form or source through which it was collected, the specific language the contact agreed to, and the campaign or list the contact is associated with.
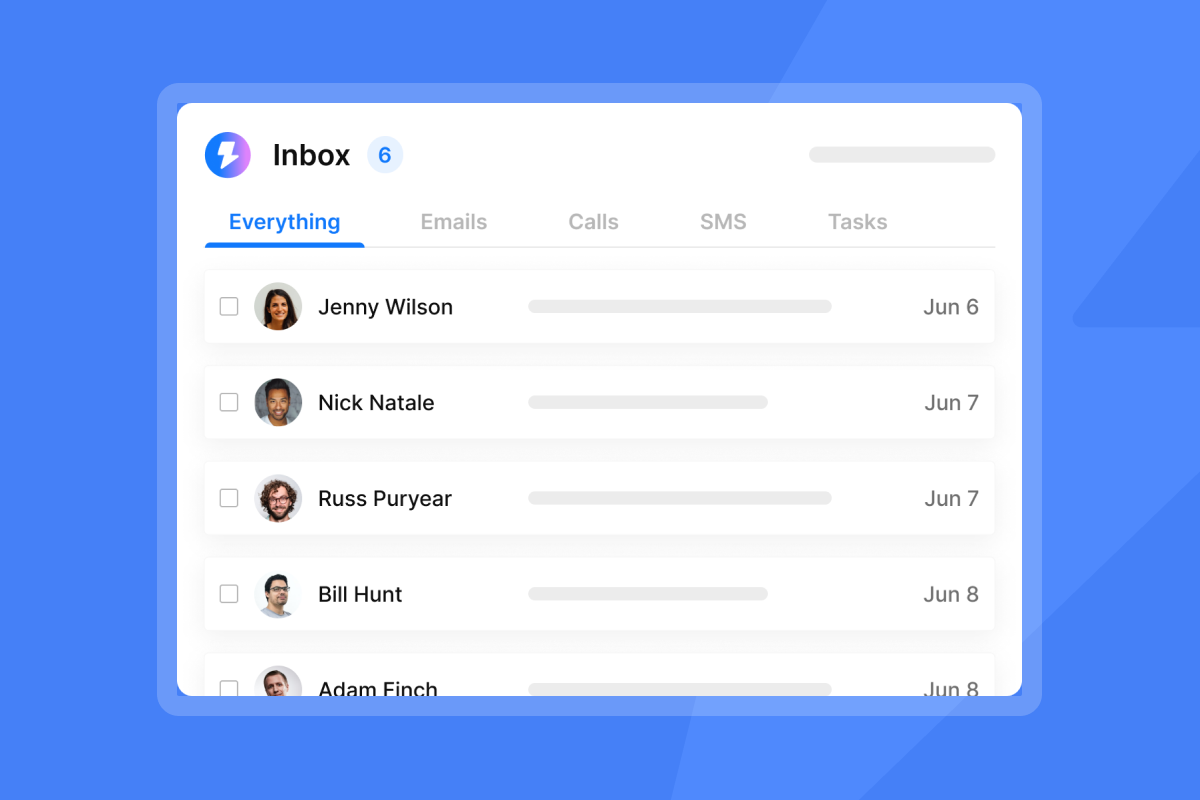
Instantly's Unibox tracks all reply and engagement history in a centralized inbox, and the HubSpot and Salesforce integration via OutboundSync automatically logs email activity to CRM contact records. This creates a timestamped activity trail that supports compliance audits without requiring manual logging. For a broader look at how tracking and compliance intersect, our email tracking privacy and compliance guide covers GDPR and CCPA obligations in detail.
Applying legitimate interest for B2B compliance
Legitimate Interest (LI) is a lawful basis under GDPR that lets you process personal data without explicit consent, provided you can demonstrate that your interests in doing so do not override the individual's rights. For B2B cold email, it is the most commonly relied-upon legal basis when dealing with professional contacts. It does not give you blanket permission. You must complete and document a Legitimate Interest Assessment (LIA) before relying on it.
GDPR legitimate interest requirements
The ICO states that you can use direct marketing as a legitimate interest, but this does not mean all direct marketing automatically qualifies. You must still demonstrate that your specific use case meets the three-part test and that you have considered the privacy impact on the individuals you're contacting.
Balancing test: your interests vs. recipient rights
The three-part LIA test breaks down as follows:
- Purpose test: Is there a legitimate interest behind the processing? Example pass: you sell accounting software and are targeting finance VPs at mid-market companies. Example fail: you are targeting personal Gmail addresses with no professional context.
- Necessity test: Is processing personal data necessary to achieve that purpose? Example pass: email is the most direct and proportionate way to reach a professional contact about a product relevant to their role. Example fail: you already have another compliant channel to reach them and are adding email purely to cast a wider net.
- Balancing test: Do your legitimate interests override the individual's interests, rights, and freedoms? Example pass: a finance VP contacted once about accounting software relevant to their role carries low privacy impact. Example fail: contacting the same person fifteen times across multiple campaigns with no connection to their role. Proportionality is the governing principle.
Build your LIA compliance record
Complete this before launching any campaign that relies on Legitimate Interest as its legal basis:
- Define the purpose: Document exactly what you are promoting and why it is relevant to the recipients' professional roles.
- Confirm necessity: Record why email is the appropriate channel for this specific outreach and why other channels are less suitable.
- Assess impact: Note the likely privacy impact on recipients, including how many touches they will receive and whether the content matches their role.
- Document reasonable expectations: Record why a contact in this role at this type of company would reasonably expect to receive outreach like this.
- Add opt-out method: Confirm that every email in the sequence contains a functional, clearly labeled unsubscribe link.
- Store the record: Store the completed LIA in a shared compliance folder accessible to your RevOps and legal stakeholders, with the date completed and the campaign it covers.
Real-world B2B legitimate interest examples
A pass: a SaaS company sends a single cold email to a VP of Operations at a 50-person logistics company, offering a warehouse management tool, with a clear opt-out link and sender identification. The product is relevant to the role, the frequency is proportionate, and the email meets CAN-SPAM identification requirements.
A fail: the same company purchases a list of 50,000 contacts, sends a daily sequence across thirty days without a documented LIA, and includes contacts with no clear role relevance to the product. The volume, lack of role targeting, and absent documentation all undermine the legitimacy of the interest.
Vetting data sources: essential vendor queries
Your compliance burden does not end with your own assessment. When a vendor's sourcing methods are opaque or non-compliant, they transfer risk to you. Before purchasing any list, run a structured vetting process.
Vendor's data sourcing methods
Ask these verification questions before signing any data contract:
- "Can you list every channel through which you source contact data, including what proportion comes from public records, partnerships, and user-submitted information?"
- "Can you provide sample consent documentation for contacts in this list before purchase?"
- "What is your process for removing contacts who have opted out from any partner's mailing list, and how quickly does that propagation happen?"
When vendors respond with vague references to "proprietary methods" or refuse to provide consent documentation, treat that as a disqualifying signal.
Audit vendor's consent and basis
Request the following documentation from any new data vendor:
- A written statement of the legal basis claimed for each contact category in the list.
- Sample consent records or LIA documentation that covers the contacts you're purchasing.
- Their sub-processor list and data transfer agreements if contacts are EU-based.
- Their data breach notification policy and timeline.
Compare these against Instantly's Data Processing Agreement as a reference for what transparent, compliant data processor documentation looks like.
How fresh is your B2B email data?
B2B contact data decays at roughly 2.1% per month, accumulating to approximately 22.5% annually. This is driven by job changes, company restructuring, and email address updates, with some analyses showing email decay accelerating to 3.6% in a single month during late 2024.
If you purchased a list twelve months ago, it could now have a 22% or higher invalid contact rate before you've sent a single email. When you send to invalid addresses, you drive up your bounce rates, damage your sender reputation, and hurt inbox placement.
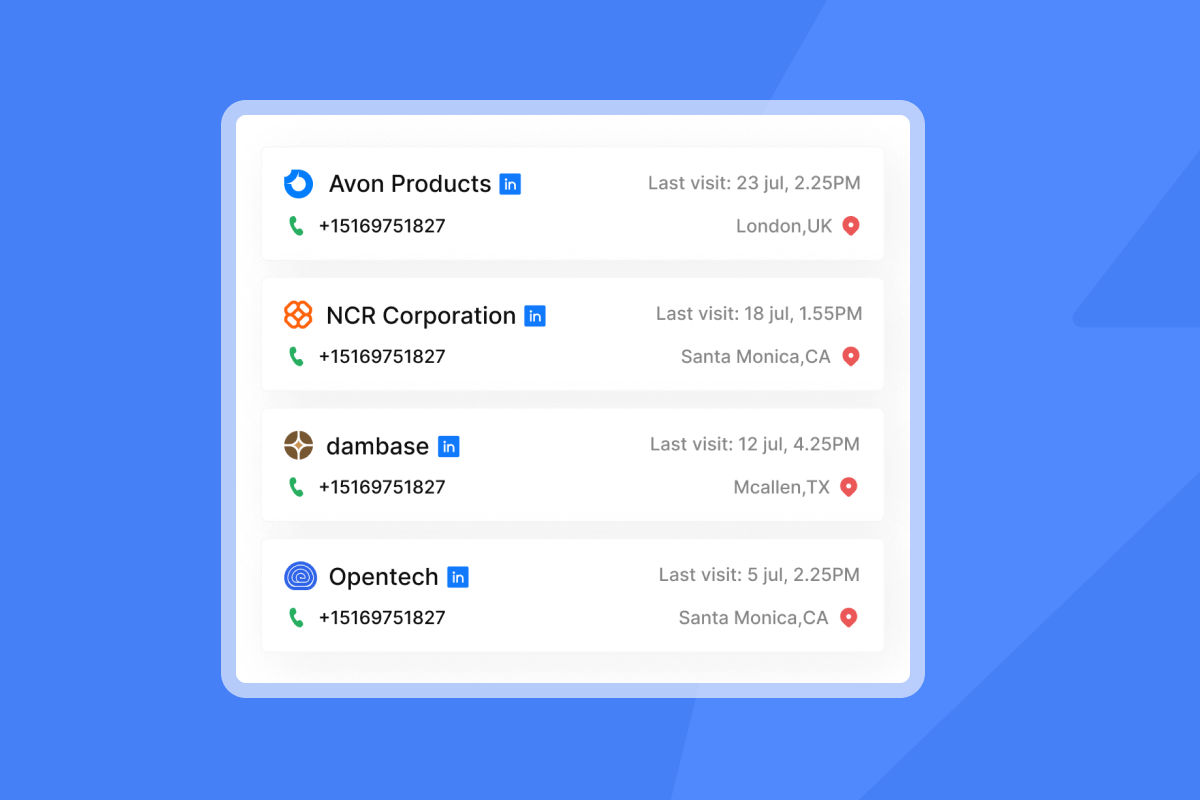
Instantly's SuperSearch addresses this directly, its 450M+ contact database runs real-time waterfall enrichment across 5+ data providers to return verified results. If the first provider can't return a verified work email, the system moves to the next until verified contact information is found or all sources are exhausted. No credits are consumed when a verified work email cannot be located, which keeps your credit spend tied to usable data. The B2B Lead Generation Guide covers how to structure list sourcing alongside campaign setup in practice.
"I like Instantly for B2B lead finding, which really works well for me... Instantly analyzes my campaigns and helps develop creative campaigns to boost my sales." - akansha K. on G2
Spotting vendor privacy risks
Walk away from a vendor immediately if you observe any of these patterns:
- Pricing far below market: A list of 10,000 verified B2B contacts for $99 signals that verification and compliance documentation are absent.
- "Proprietary acquisition methods" without specifics: This phrase substitutes for consent documentation rather than explaining sourcing.
- Guaranteed performance claims: Promises of guaranteed open rates or zero bounces signal dishonest data quality representations.
- No sub-processor documentation: Any vendor processing personal data of EU residents must name their sub-processors and data transfer mechanisms.
- Personal email domains in a B2B list: Presence of Gmail, Yahoo, or Hotmail addresses in a list sold as "B2B contacts" signals unsegmented or uncleaned data.a
Opt-out management is where legal compliance meets operational reality. Honoring unsubscribe requests promptly is both a legal requirement and a deliverability protection. Contacts who cannot easily opt out file spam complaints instead, and spam complaints are the fastest way to damage your sender score. Our email tracking software for bulk outreach guide covers how to scale these safeguards across SDR teams.
One-click unsubscribe legal mandates
Under CAN-SPAM, you must include a clear and conspicuous opt-out mechanism in every commercial email. Your unsubscribe mechanism must work for at least 30 days after you send the message, and you must process the request within 10 business days. You cannot require the recipient to pay a fee, provide information beyond an email address, or take more than one step to unsubscribe.
CASL mirrors the 10-business-day window and requires you to make unsubscribe mechanisms free, simple, and functional. Under GDPR, you must process data subject requests within 30 days of receiving them (extendable to 90 days in complex cases), so actioning opt-outs from marketing communications promptly is both a legal requirement and a practical necessity for any organization processing EU personal data.
Processing unsubscribe requests on time
A reliable opt-out workflow looks like this:
- Contact clicks the unsubscribe link in the email.
- The contact is added to your global suppression list as quickly as possible.
- The CRM record is updated with an opt-out flag within the legally required window (10 business days for CAN-SPAM and CASL, 30 days for GDPR).
- The suppression event is logged with a timestamp and the campaign it originated from.
- A periodic audit confirms the suppression list propagates correctly across all active campaigns.
Instantly's global block list covers your entire workspace, which means any contact added to it cannot be emailed by any team member across any campaign. Campaign-level suppression only prevents re-contact within a single sequence, but the global block list stops all re-contact across every campaign.
The automated inbox placement testing feature complements this by flagging deliverability issues before they become blocking problems. Running regular automated inbox placement tests helps you catch reputation damage early, before it compounds into a full blacklist event.
Preventing re-contact after opt-out
CRM integration is your operational safeguard that prevents opted-out contacts from re-entering campaigns via list uploads. The HubSpot and Salesforce integration via OutboundSync syncs email activity, including unsubscribe events, back to the CRM contact record. When a contact is marked as opted out in the CRM, they cannot be re-imported into a campaign without the suppression flag triggering a block.
"The unibox is really clean and organizes my replies all in one place in such a user-friendly manner. Instantly allows me to connect hundreds of inboxes and send mass emails on a scheduled basis, automatically organizing which inbox to send with on which day and spreading it all out." - Harvey S. on G2
For teams not using OutboundSync, Zapier and Make integrations are available to build custom suppression sync workflows between Instantly and your CRM of choice. Our email tracking integrations guide covers how to connect these workflows without creating data silos.
Privacy audit checklist for B2B email programs
Run a privacy audit quarterly to protect yourself from the compounding effects of data decay, roster turnover, and regulatory changes. Assign each area to a specific role so accountability is clear.
Audit email list data privacy
- Confirm the original source and collection date for every active list segment.
- Run a list hygiene check to remove hard bounces, invalid addresses, and known spam traps.
- Verify that all active contacts have a documented legal basis for outreach.
- Remove contacts with zero engagement after 12-18 months unless active re-engagement cadences are in place.
Consent and legitimate interest records
- Store LIA documents in a named folder in your shared drive, organized by campaign and date.
- Confirm each LIA covers the Purpose, Necessity, and Balancing tests.
- Date-stamp every LIA and link it to the specific campaign it covers.
- Review LIAs whenever a campaign targets a new segment or geographic market.
How to vet email list vendors
Use this quick checklist for any new data partner:
- Can they name their data sources by channel?
- Do they provide sample consent records on request?
- Do they have a published sub-processor list?
- Can they confirm data collection dates for the specific segment you're buying?
- Do they have a documented process for removing opted-out contacts from their database?
- Have they confirmed GDPR, CAN-SPAM, and CASL compliance in writing?
Assign privacy roles and responsibilities
You prevent gaps with clear ownership. A workable structure for a 5-15 rep team:
- Individual reps: responsible for not importing contacts without a documented legal basis and for escalating opt-out requests immediately rather than handling them manually.
- RevOps or Sales Ops Manager: owns the LIA documentation process, vendor contracts, and quarterly audits.
- SDR Team Lead: responsible for enforcing send limits (cap at 30 emails per inbox per day), monitoring bounce rates, and flagging anomalies.
- Individual reps: responsible for not importing contacts without a documented legal basis and for escalating opt-out requests immediately rather than handling them manually.
Navigating B2B email list regulations
Regulation | Applies to | Prior consent required | Opt-out window | Legitimate interest available |
|---|---|---|---|---|
GDPR (EU/UK) | EU and UK contacts | No, but lawful basis required before sending | Data subject requests within 30 days | Yes, with documented LIA |
CAN-SPAM | US commercial email | No | 10 business days | N/A |
CASL | Contacts in Canada | Yes (express or implied) | 10 business days (verify current requirements) | Not available |
B2B email consent requirements summary
Regulation | Applies to | Prior consent required | Opt-out window | Legitimate interest available |
|---|---|---|---|---|
GDPR (EU/UK) | EU and UK contacts | No, but lawful basis required before sending | Within 30 days | Yes, with documented LIA |
CAN-SPAM | US commercial email | No | 10 business days | N/A |
CASL | Canadian recipients | Yes (express or implied) | 10 business days | No |
Compare GDPR and CAN-SPAM for B2B email
Both GDPR and CAN-SPAM require you to include sender identification and a functional unsubscribe mechanism in every commercial email. The differences are significant for how you structure your pre-send process.
Under GDPR, you need a documented lawful basis before sending your first message. For B2B cold email, you typically use Legitimate Interest, which requires a completed LIA. The ICO also requires that your processing does not override the individual's privacy rights, which in practice means keeping send frequency proportionate and targeting contacts whose roles are directly relevant to your offer.
CAN-SPAM does not require you to get prior consent. You must ensure that the From, To, Reply-To, and routing information accurately identify you as the sender, that your subject line reflects the email content, that you identify the message as an advertisement unless a prior relationship exists, that you include your physical address, and that you provide and honor a functional opt-out mechanism within 10 business days.
Under CASL, you can use implied consent only when a prior business relationship exists or the contact has publicly published their email without a no-contact statement, and your message relates directly to their professional role.
One important update: as of January 1, 2023, the California Privacy Rights Act (CPRA) removed the prior B2B exemption that had previously excluded business contact data from California Consumer Privacy Act obligations. California-based B2B contacts must now be treated with the same opt-out rights and data minimization principles as consumer data under CPRA requirements.
Purchased B2B lists: compliance guide
When you buy a list, you do not inherit the vendor's legal basis. You must independently assess whether your use of the data meets your own legal obligations. Steps before using any purchased list:
- Request the vendor's data sourcing and consent documentation.
- Segment the list by geography to identify which regulations apply.
- Complete your own LIA for each geographic segment covered by GDPR.
- Confirm CAN-SPAM identification requirements are in place for US outreach.
- For any Canadian contacts, verify implied or express consent documentation before sending.
- Load the verified list into Instantly and enable the global block list check before launching.
You should keep prospect data only for as long as is reasonably necessary for the stated outreach purpose. The CPRA's data minimization requirements explicitly prohibit collecting or retaining personal information beyond what is necessary for disclosed purposes. A workable policy for most B2B outreach programs:
- Remove contacts with zero engagement after 12-18 months.
- Delete or anonymize contacts who have requested erasure within 45 calendar days, after acknowledging receipt of the request within 10 business days, as required under CPRA.
- Review and purge stale segments annually as part of your privacy audit.
Handling B2B privacy complaints
The real question for every outbound sales leader is this: can you hand your list sourcing documentation, your LIA records, and your opt-out logs to an auditor today and have them withstand scrutiny? If the answer is no, the audit checklist above is your starting point.
Try Instantly demo and its SuperSearch to access 450M+ verified B2B contacts with built-in waterfall enrichment, or review our email tracking guide to assess where your current compliance gaps are creating the most risk.
Read next
- Email deliverability for sequences: warmup, health monitoring, and compliance
- Email tracking privacy and compliance: the sales leader's guide to GDPR and CCPA
- Email tracking integrations: how to sync CRM, calendar, and workflows without data silos
FAQs
How long do I have to process an opt-out request under CAN-SPAM?
You must honor opt-out requests within 10 business days of receipt under CAN-SPAM. You cannot charge a fee or require any action beyond submitting an email address to complete the unsubscribe.
What is a Legitimate Interest Assessment in B2B cold email?
A Legitimate Interest Assessment (LIA) is a three-part documented test (Purpose, Necessity, Balancing) that confirms your grounds for processing personal data without explicit consent under GDPR. You must complete and store an LIA before sending cold outreach to EU or UK contacts using Legitimate Interest as your lawful basis.
Does GDPR apply to B2B cold email lists?
Yes. GDPR covers the personal data of any individual located in the EU or UK, including business contacts. You need a documented lawful basis, typically Legitimate Interest with a completed LIA, before sending to any contact in those jurisdictions.
How fast does B2B email data decay?
B2B contact data decays at approximately 22.5% per year according toindustry research, driven by job changes, company restructuring, and email address updates. Lists older than 12 months without re-verification carry significant bounce risk that will damage your sender reputation.
Do I need consent to cold email someone in the US?
CAN-SPAM does not require prior consent for commercial email to US recipients. You must include sender identification, a physical address, and a working opt-out mechanism, and you must process opt-out requests within 10 business days.
Key terms glossary
Legitimate Interest Assessment (LIA): A documented evaluation of three tests (Purpose, Necessity, and Balancing) that you must complete before relying on Legitimate Interest as a lawful basis for processing personal data under GDPR. It must be stored and linked to the specific campaign it covers.
Zero-party data: Information a contact voluntarily and proactively shares with your organization, such as through a form, survey, or event registration. It carries the strongest compliance standing because the contact initiated the data exchange.
Global block list: An account-wide suppression list in your outreach tool that prevents any team member from sending to opted-out or blocked contacts across all campaigns. In Instantly, the global block list covers the entire workspace, not just individual sequences.
Data lineage: The documented trail of where a contact's data originated, how it was collected, what verification or enrichment steps were applied, and any modifications made over time. Maintaining data lineage is a practical prerequisite for compliance audits and a requirement of sound data governance practice.
Waterfall enrichment: A data verification method that queries multiple data providers in sequence until a verified result is found. Instantly's SuperSearch uses waterfall enrichment across 5+ providers to return verified work emails, consuming credits only when a verified result is returned.





